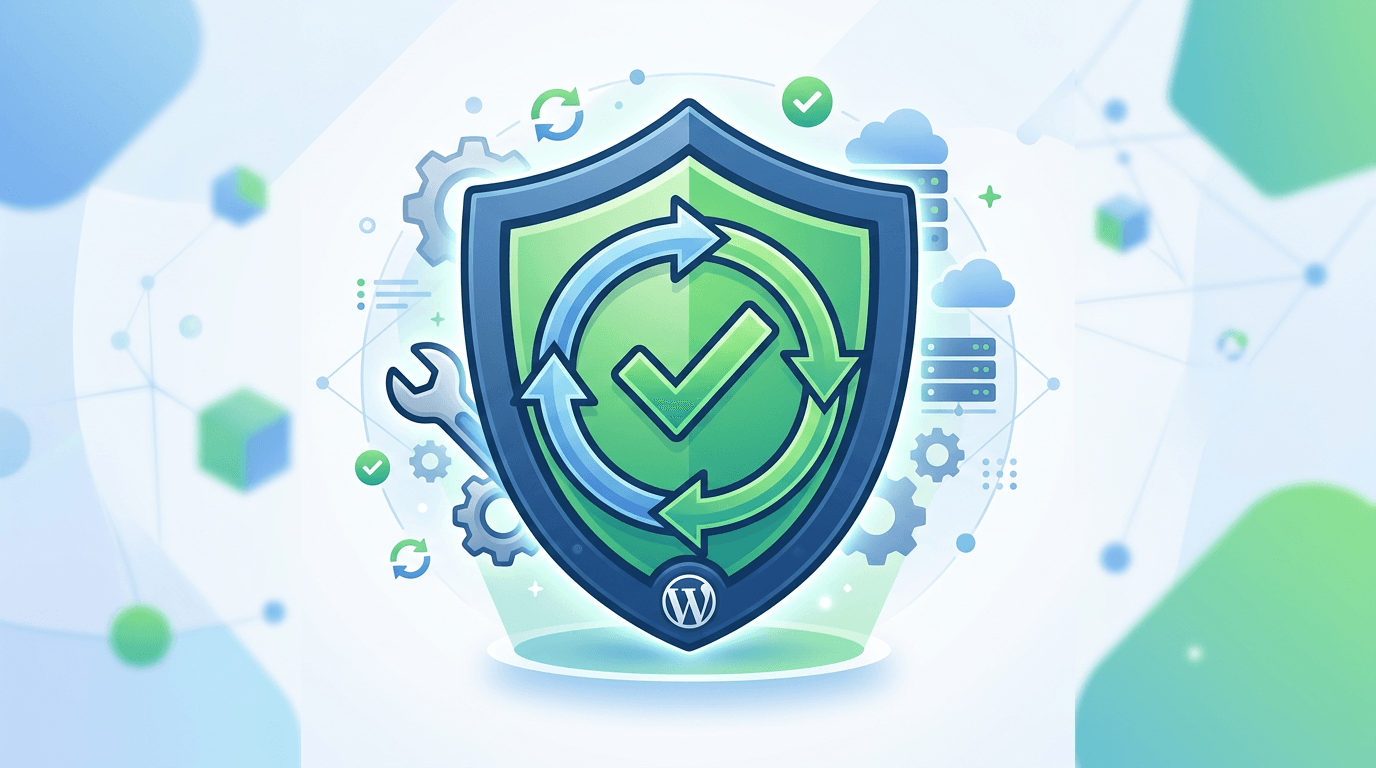
WordPress maintenance is not a cosmetic chore or an optional line item for “technical people.” It is the operating rhythm that keeps a dynamic publishing platform secure, fast, and trustworthy for customers, editors, and administrators. Unlike a static HTML brochure, WordPress is composed of core software, a theme, and plugins—each maintained by different teams on different schedules. When updates lag, attackers probe known vulnerabilities. When updates rush without testing, checkout breaks. This article explains why maintenance is structurally necessary, what a mature maintenance program includes, how staging and backups reduce risk, and how to communicate maintenance value to non-technical stakeholders without drowning them in jargon.
You will learn how to categorize updates by risk, how to build a testing matrix around revenue-critical flows, why database hygiene belongs in maintenance, and what signals indicate your organization has outgrown ad hoc patching. The objective is practical: a maintenance model you can run internally or confidently outsource—without surprises.
Why WordPress is inherently dynamic—and why that matters
Every WordPress request executes code paths that can change behavior based on configuration, user role, active plugins, and theme templates. That dynamism enables rich features: memberships, commerce, multilingual content, editorial workflows, and integrations. It also means the system surface area grows with each plugin. A static site has a comparatively fixed attack surface; WordPress changes whenever a vendor ships a new release.
Security updates are time-sensitive, not convenience updates
Security releases address publicly disclosed vulnerabilities. Delaying updates increases exposure as exploit code becomes commoditized. Yet “update immediately everywhere” can be reckless without backups and smoke tests. Mature teams triage: patch critical remote-code vulnerabilities faster than minor informational leaks, but never confuse triage with indefinite delay.
Compatibility testing: the hidden cost of flexibility
Plugins interact through hooks, shared libraries, and database assumptions. A WooCommerce update may conflict with a custom shipping plugin. A block editor enhancement may clash with a legacy shortcode workflow. Maintenance includes staging verification: run updates on a copy, test key journeys, then promote to production with rollback readiness.
Backups: the non-negotiable foundation
Backups must include files and database together, be stored off-server, and be periodically restored in a test environment to prove they work. Untested backups are hope, not strategy. Incremental backups help large media libraries; retention policies should cover “we did not notice corruption for two weeks” scenarios.
Staging environments that earn trust
Staging should mirror production closely: PHP version, extensions, memory limits, and caching behavior. If staging disables object cache that production relies on, you will ship false confidence. Align environments deliberately, document differences, and adjust tests accordingly.
Database hygiene as maintenance, not spring cleaning
Revisions, spam comments, orphaned meta, stale transients, and leftover options from retired plugins accumulate. Periodic hygiene reduces backup size, speeds queries, and lowers surprise interactions between old data and new code. Major migrations—especially page builder changes—should trigger a scheduled database review.
Monitoring, logs, and incident response
Uptime monitors catch outages; error logs catch fatals; security scanners catch malware. Maintenance includes reviewing these signals on a cadence and tuning alert noise so real incidents surface. After incidents, capture root cause and feed improvements into the next maintenance sprint.
Roles and responsibilities in larger teams
Clarify who approves plugin installs, who runs updates, who validates commerce, and who owns vendor relationships with agencies or hosts. Without ownership, updates slip or duplicate effort creates conflicting changes.
Communicating maintenance to executives
Frame maintenance as risk reduction and revenue protection: fewer checkout incidents, fewer SEO crises from hacked redirects, faster editorial throughput. Pair qualitative stories with quantitative metrics: mean time to restore, number of critical vulnerabilities patched within SLA, and post-update defect rate.
Maintenance calendars: weekly, monthly, quarterly
Weekly tasks might include reviewing failed logins, checking backups, and scanning for plugin updates with security notes. Monthly tasks include staging tests for non-critical updates and reviewing plugin inventory for redundancy. Quarterly tasks include deeper performance reviews, access audits, and disaster recovery drills.
When “just update everything” fails
Some hosts offer auto-updates. They help until they do not—silent breakage on custom code paths is painful. Prefer controlled batches with notes, especially for WooCommerce, LMS, and membership stacks.
Legal and compliance considerations
Some industries require change logs, access trails, and retention policies. Maintenance processes can satisfy these requirements when designed intentionally rather than as afterthoughts.
Frequently asked questions
Can I skip updates if my site is small?
Small sites are still scanned by bots at scale. Size does not grant immunity.
How do I balance speed and safety?
Use staging, automate backups, and batch updates by risk class.
Is managed hosting enough?
Hosting layers help, but application-level testing remains your responsibility for custom themes and plugins.
How Duppins Technology delivers maintenance
Duppins Technology combines scheduled updates, staged verification, performance and database hygiene, and clear reporting so WordPress stays secure without turning every Friday into roulette.
Key takeaways
- WordPress maintenance is structural, not optional cosmetic work.
- Security updates need SLAs; compatibility needs staging tests.
- Backups must be tested; staging must mirror production meaningfully.
- Database hygiene prevents slow surprises after migrations.
- Governance and communication turn maintenance into a business asset.
Building a risk matrix for releases
Classify updates into tiers: critical security patches, minor point releases, major version jumps, and ecosystem updates that touch payments or identity. Each tier gets a different testing depth and deployment window. Critical patches may deploy faster with narrower tests but still require rollback readiness. Major jumps schedule longer staging cycles and cross-team sign-offs. Document criteria so on-call engineers do not improvise under pressure.
Dependency mapping across plugins
Maintain a simple map: which plugins touch checkout, which touch SEO canonicals, which inject headers, which modify roles. When an update ships for one node, consult the map to identify cross-tests. This living document prevents the classic blind spot where a shipping plugin update silently breaks a donation form because nobody remembered the fragile hook order.
Editorial continuity during maintenance windows
Communicate freeze periods when needed, but prefer rolling updates that avoid blocking publishing. If cache purges or CDN propagations delay visibility, tell editors what to expect. Reducing mystery prevents duplicate publishes and accidental conflicts.
Post-incident reviews that improve the system
After any outage or rollback, run a lightweight postmortem: timeline, root cause, detection gap, and remediation tasks with owners. Feed tasks into the next maintenance sprint so patterns improve instead of repeating.
Vendor coordination
Themes and plugins sometimes require coordinated updates. Read release notes together, not in isolation. If a vendor deprecates a function your custom code relied upon, schedule paired updates rather than hoping order does not matter.
Closing perspective
Maintenance is how you keep WordPress feeling dependable: editors trust publishing, customers trust checkout, and leadership trusts the web channel as a growth engine rather than a fragile science project.
Operational playbooks for predictable maintenance windows
Define a standard window with owners named in advance: backup verification, staging pull, plugin batch one, smoke tests, plugin batch two, production deploy, post-deploy checks, and cache purge validation. Use checklists rather than memory—tired humans skip steps. Record versions before and after each batch so diffs are obvious if something regresses a week later. Keep a rollback script: database snapshot restore plus known-good file release tag. Practice rollbacks quarterly so muscle memory exists when incidents strike at inconvenient hours.
Access control and least privilege
Maintenance includes identity hygiene: remove former contractors, enforce two-factor authentication for administrators, rotate application passwords used by integrations, and audit API keys stored in options tables. Overprivileged accounts turn a minor XSS into a site takeover. Pair technical controls with process controls: who can install plugins, who can export customer data, and how those actions are logged.
Performance regression checks belong in maintenance
Each maintenance cycle should include three Lighthouse URLs and a quick scan of TTFB medians. Many performance regressions arrive through plugin updates that add scripts or alter queries. Catching them early avoids month-long SEO drifts while leadership wonders why bounce rates climbed.
Content freeze policies that respect marketing reality
Hard freezes during holiday peaks may be necessary, but blanket bans on updates create security debt. Prefer rolling updates of low-risk components while deferring risky theme refactors. Communicate clearly: “Security patches still apply; feature freezes on templates only.” Alignment prevents shadow IT where marketers install unvetted plugins on production to meet deadlines.
Documentation debt is maintenance debt
Maintain a short architecture note: hosting stack, caching plugin, critical integrations, cron jobs, and custom mu-plugins. When the primary engineer is unavailable, others can still execute updates safely. Update the doc whenever environment variables change or new webhooks appear.
Disaster recovery drills
Simulate failure: restore backup to an isolated environment, change DNS in a lab if possible, and measure recovery time objectives. Drills reveal missing credentials, broken off-site storage, or incompatible PHP versions faster than real disasters do.
Integrations and headless consumers
If mobile apps or decoupled frontends consume WordPress APIs, maintenance must include contract tests for those endpoints. A harmless-looking core update can alter REST pagination defaults or field shapes. Automated smoke tests against staging catch surprises before mobile releases ship.
Long-term vendor relationships
Choose plugins with sustainable release cadences and transparent security policies. When a vendor goes quiet, plan migrations proactively rather than waiting for a PHP fatal on upgrade day. Maintenance strategy includes lifecycle planning, not only button clicking.
Executive dashboards that stay honest
Report mean time to patch critical issues, number of failed staging tests that prevented bad deploys, and percentage of updates applied within SLA. Those metrics prove maintenance prevents incidents rather than “doing nothing visible.”
Final checklist for internal teams
- Tested backups and documented restores
- Staging parity checklist completed monthly
- Risk-tiered update calendar published
- Commerce and forms smoke tests after each batch
- Access audits quarterly
- Performance spot checks after releases
Change management for agencies and distributed teams
When multiple teams ship simultaneously, WordPress becomes a collision surface: a theme developer ships new templates while a marketer activates a plugin that alters query loops, while operations schedules PHP upgrades. Maintenance governance coordinates these streams. Require pull requests for custom PHP and mu-plugins, tag releases with semantic versions, and pair Git rollbacks with database snapshots when schema-changing plugins update. Treat Advanced Custom Fields exports, block pattern JSON, and global style changes as production changes—they deserve review and staging validation just like code because they alter runtime behavior for every visitor.
PHP version readiness and deprecation hygiene
Hosts sunset old PHP versions on predictable cadences. Maintenance includes reading deprecation notices in logs, upgrading or replacing plugins that rely on removed functions, and validating WP-CLI scripts, cron endpoints, and legacy XML-RPC paths if they remain enabled. Proactive readiness prevents the emergency weekend where a host flips PHP and half the stack fatals because one abandoned utility plugin was forgotten in the mu-plugins directory.
Media libraries, CDN offloading, and restore-time risk
Upload folders grow without bound. Large libraries inflate backup duration, increase restore-time risk during incidents, and complicate migrations. Maintenance should include editor guidance on image sizing, periodic review of orphaned attachments after content migrations, and verification that CDN offloading rules still match the active domain and SSL certificates. Storage is not infinite; cost and operational drag compound quietly until a restore window becomes unacceptable for leadership.
Action Scheduler, WP-Cron reliability, and invisible failures
WooCommerce and many modern plugins enqueue background work through Action Scheduler. Queues can stall when cron is unreliable, disk fills, or database locks contend. Maintenance includes monitoring queue depth, switching busy sites to real system cron, and alerting when jobs fail repeatedly. Invisible failures show up late—as missed renewal emails, stuck imports, or inventory drift—long after the original regression shipped.
Hardening that complements patching
Patching closes known vulnerabilities; hardening reduces blast radius between patch cycles. Use a Web Application Firewall tuned for WordPress patterns, enforce two-factor authentication for privileged roles, remove unused administrator accounts, rotate integration credentials stored in options, and disable file editing in production when policy allows. Least privilege is maintenance because access creep is how minor XSS becomes site-wide compromise.
Compliance-friendly logging and retention
Regulated environments need audit trails without storing prohibited sensitive payloads in logs. Maintenance defines what is logged, how long logs are retained, and how log pipelines survive host migrations. Disk exhaustion from runaway logs is an outage mode; rotation and monitoring belong on the same calendar as plugin updates.
Financial planning and capacity for calm maintenance
Budget for backup storage growth, monitoring tools, staging environments, and skilled hours. Underfunded maintenance converts predictable engineering into expensive emergencies, customer-visible downtime, and reputational damage. When executives see maintenance as insurance with measurable incident reduction, funding stabilizes and teams stop shortcutting staging because “we cannot afford the time.”
Editor training as an operational sensor network
Editors frequently notice subtle regressions first: broken shortcodes after a builder update, strange footer links after a partial migration, or slow saves during campaign weeks. Provide a lightweight reporting channel with a clear SLA. Human sensors augment automated scanning because many issues are brand-quality problems before they become security scanner problems.
Postmortems that actually change behavior
After incidents, run a short blameless review: timeline, detection gap, mitigation time, and concrete follow-ups with owners. Feed follow-ups into the next maintenance sprint so rollbacks get faster, monitoring improves, and documentation gaps close. Without postmortems, teams repeat the same outage shapes with different plugin names.
Vendor SLAs and escalation paths
Know how to escalate critical security issues with your host, CDN, and payment providers. Store escalation contacts outside the system that might be down. Maintenance maturity includes rehearsing those calls once a year so phone trees do not consume precious minutes during real incidents.
Closing operational reminder
Maintenance is never finished; it is a cadence. Keep calendars honest, keep backups tested, and keep staging trustworthy so every update strengthens the site instead of gambling with it.
Document owners, review dates, and rollback owners on every change ticket so accountability stays visible when schedules get busy.
Revisit the maintenance calendar after every major campaign, acquisition, or redesign because traffic shape and risk profile change, and your rhythms should change with them.
Share a simple monthly summary with leadership: patches applied, tests passed, incidents avoided, and upcoming risks so maintenance stays transparent.
Treat every maintenance window as a chance to reduce debt, not only to apply patches, and your roadmap will stay healthier quarter after quarter for everyone, including stakeholders and partners.
Maintenance is the heartbeat of a serious WordPress operation—steady, measured, and always preparing for the next change the internet will throw at you.